Refreshing the Filecoin Bug Bounty Program

Now that the Filecoin Virtual Machine (FVM) is officially live on Filecoin mainnet, the community is excited to announce a refreshed Filecoin bug bounty program, featuring increased rewards up to 500k USD for critical issues and inclusion of programmability features in scope.
Prior to mainnet deployment, the FVM core team ran a number of initiatives to analyze and harden the security of Filecoin’s new programmability components. This included internal red team audits, two external audits by Oak Security and Alex Wade, and the FVM Bulletproofing program.
Post-launch, the community continues to be committed to guaranteeing the security of the Filecoin network, now including its new and updated components: the FVM, the EVM runtime, and its dependencies.
With this update, we once again extend an invitation to security researchers, developers, and bug bunters to help us identify latent risks and problems that may remain in the codebase after mainnet launch.
Please make sure to use responsible disclosure and security best practices to minimize impact to the network, and to qualify for rewards.
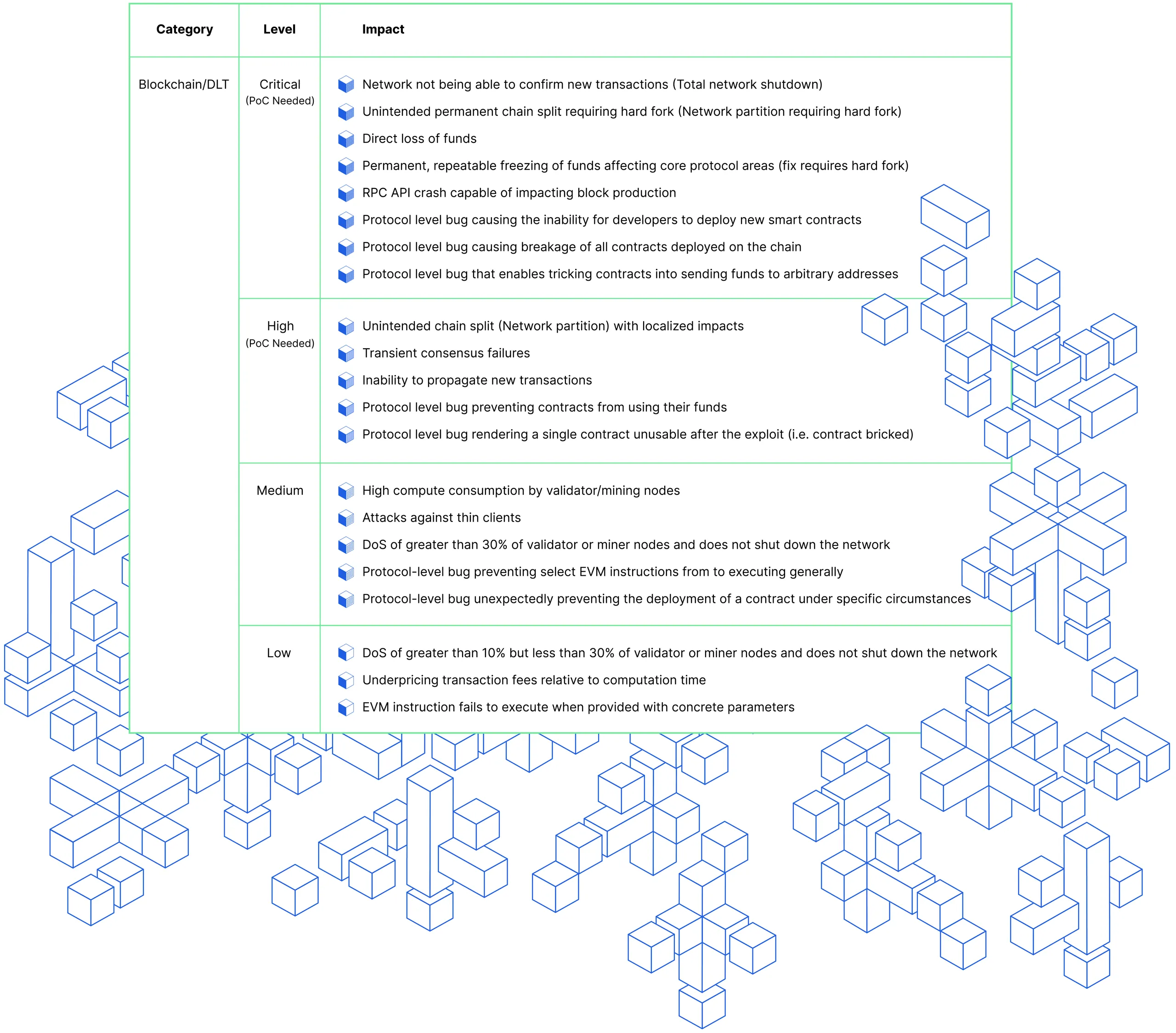
Updated Scope
Notes
- Criteria and the wording for this table might be refined in the next 5-7 working days.
- Responsible disclosures for issues not explicitly listed in the table will still be reviewed and matched up against the severity classification based on their impact.
Updated rewards
To further incentivize developers and web3 security experts, bug bounties have been raised significantly. Please find the levels based on severity below:
- Critical: up to 500,000 points
- High: up to 100,000 points
- Medium: up to 25,000 points
- Low: up to 10,000 points
- Micro-level issues: up to 5,000 points
Where currently 1 point = 1 USD (payable in USD, DAI, or FIL).
Rules and reports
The rules of the Filecoin Security Program remain intact, including what’s out of scope. To be eligible for bounties, you MUST apply responsible disclosure practices and submit your report to security@filecoin.io, following the instructions in the previous links.